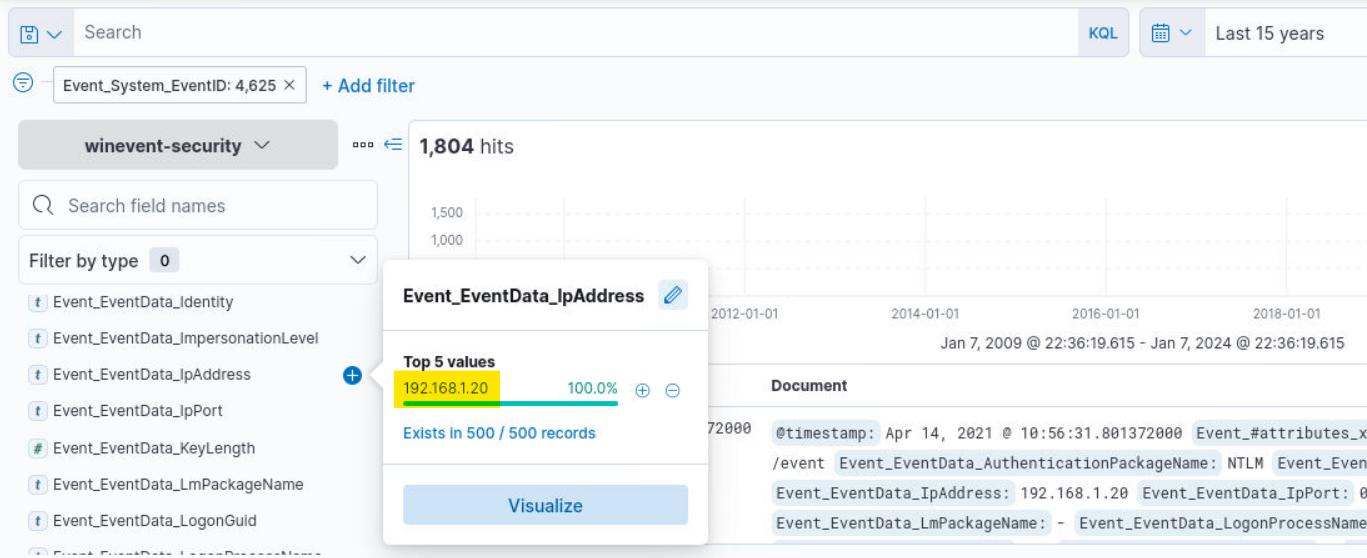
Source IPs of failed login attempts
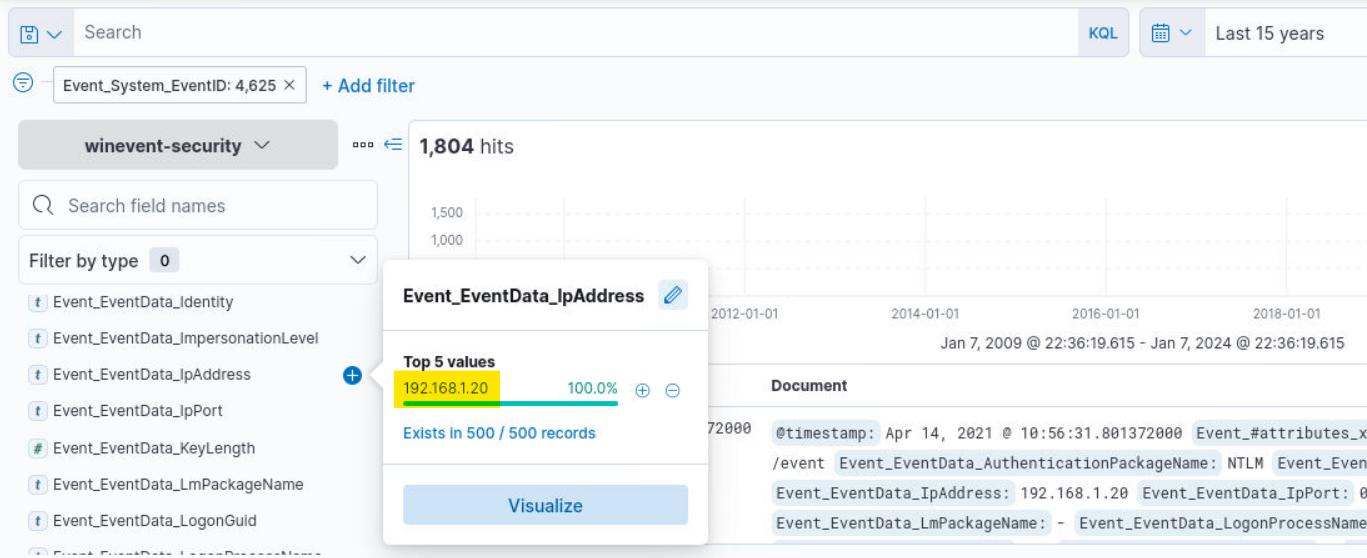
Source IPs of failed login attempts
Q&A 1
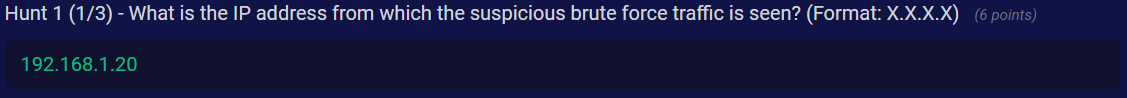
Logon types of failed login attempts
Q&A 2
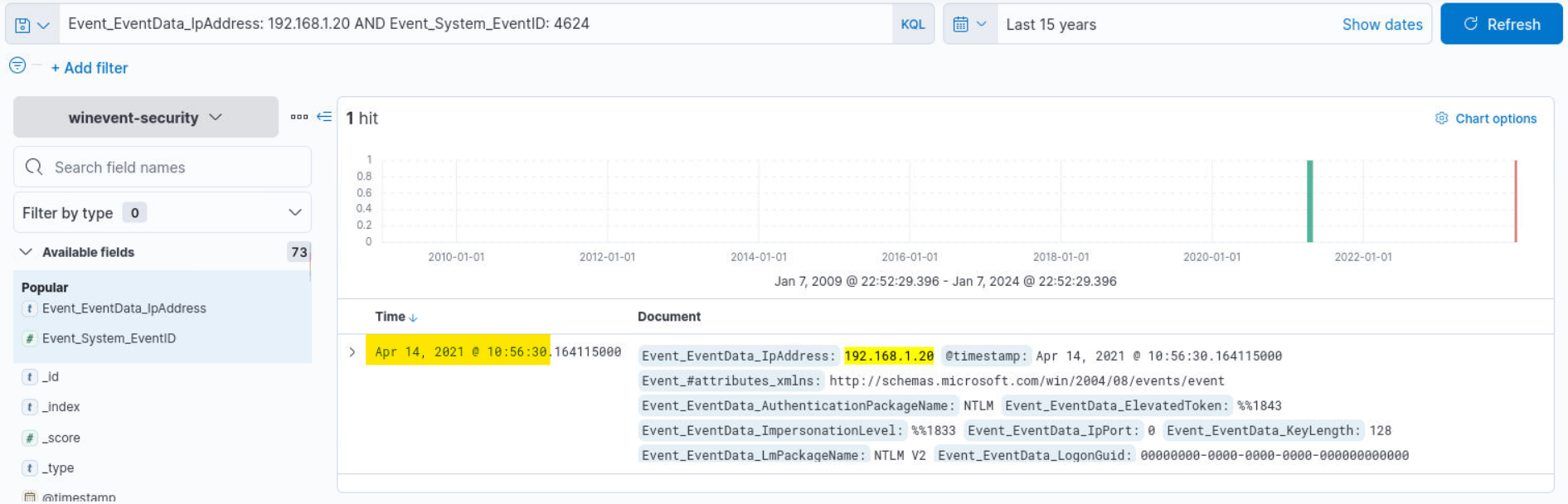
Successful logins originating from attacker's IP
Q&A 3
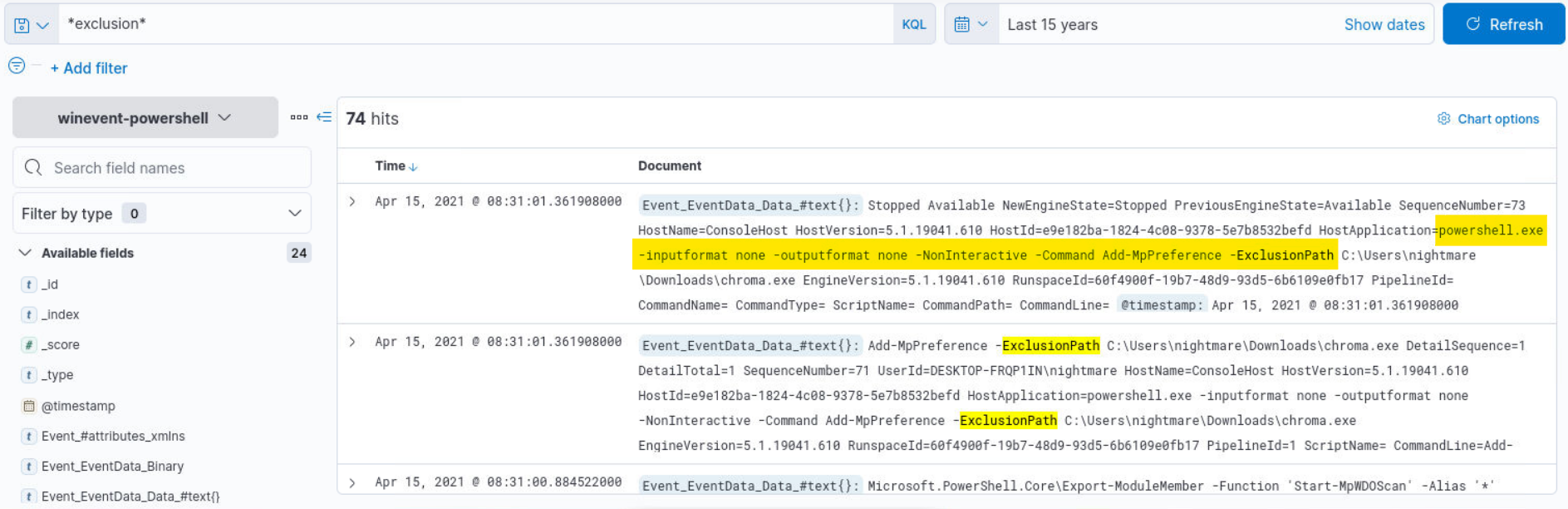
Filtering for *exclusion* to find the command used for bypassing Defender
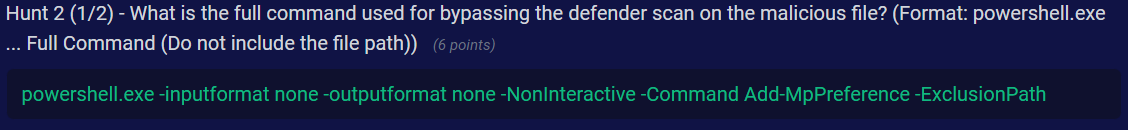
Q&A 4
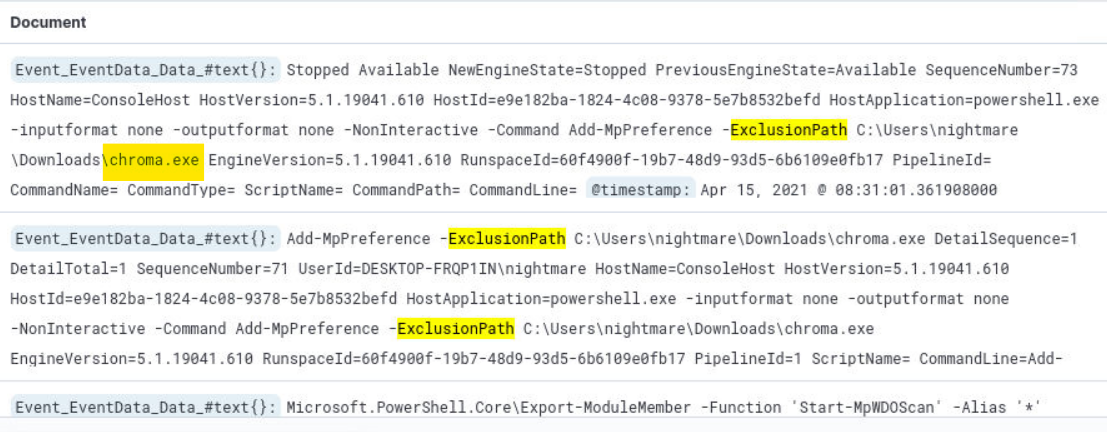
Malicious filename found in the executed command
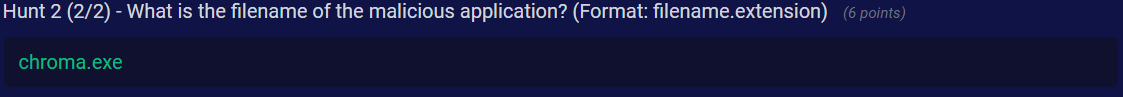
Q&A 5
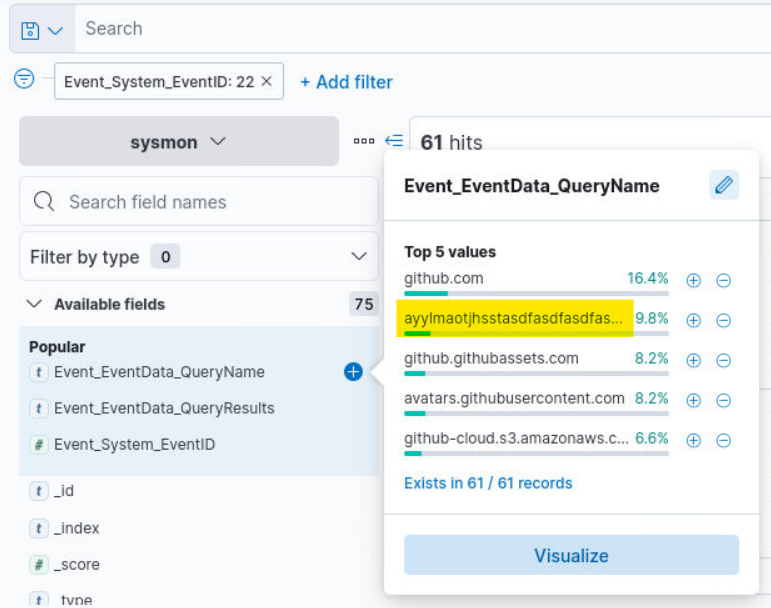
WannaCry kill switch domain found in the DNS logs
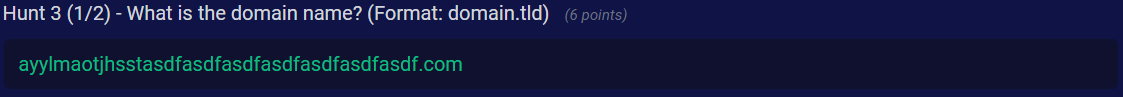
Q&A 6
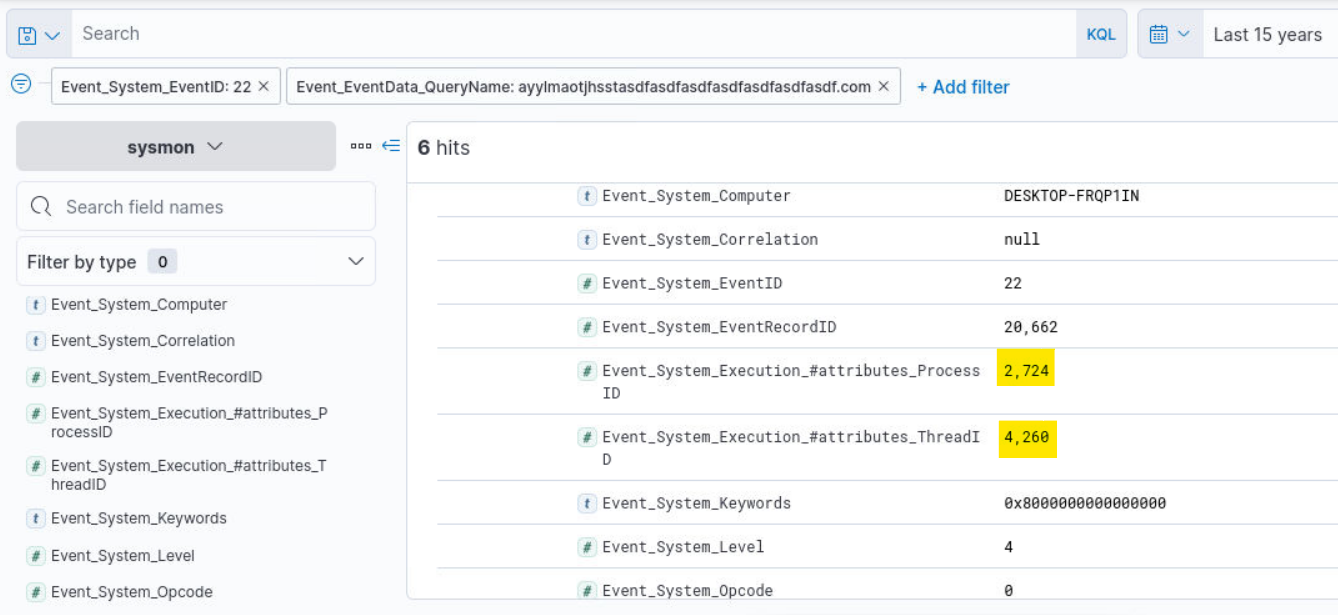
Execution PID and TID found in the DNS logs
Q&A 7
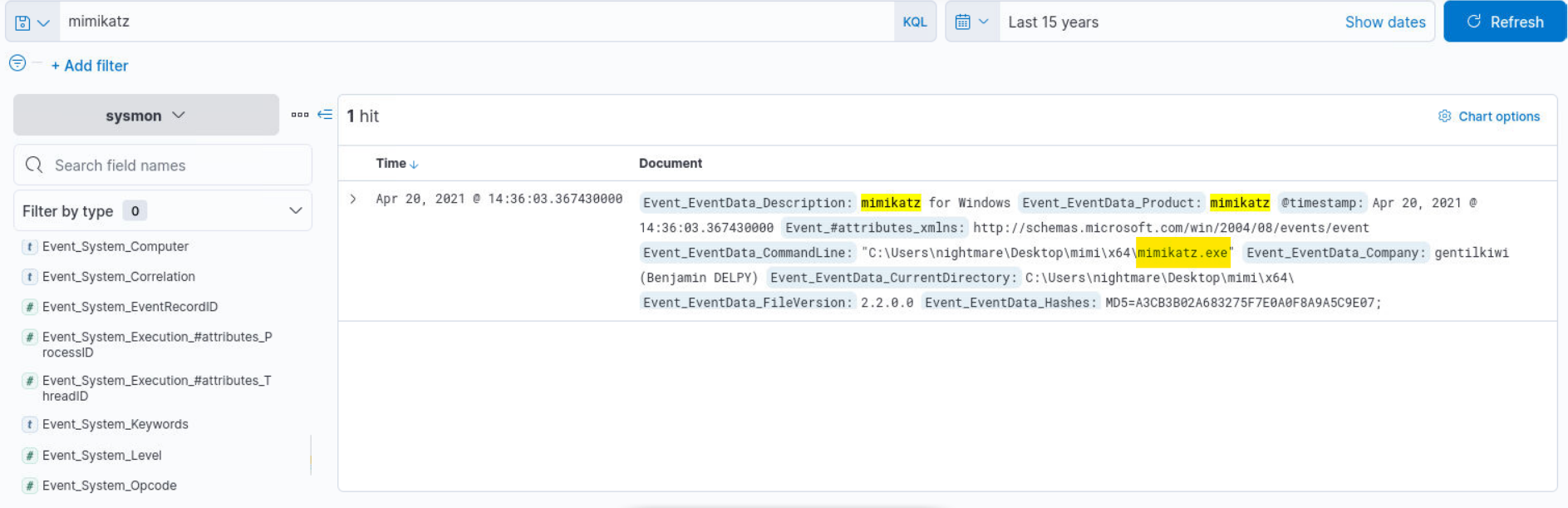
Filtering for "mimikatz"
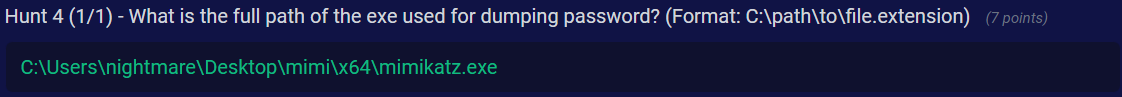
Q&A 8